Did you know that over 43% of the web is powered by WordPress? That’s right, you’re about to join the ranks of millions who’ve chosen the world’s most popular content management system to…

Did you know that over 43% of the web is powered by WordPress? That’s right, you’re about to join the ranks of millions who’ve chosen the world’s most popular content management system to…
In the dynamic world of digital marketing, the power of well-crafted content reigns supreme. Ranking-Articles.com emerges as a leader, providing exceptional content that not only engages readers but also propels websites to the…

In today’s digital landscape, encountering the ERR_CONNECTION_RESET error can disrupt the seamless flow of online activities. For those seeking innovative solutions to this challenge, understanding the underlying causes and implementing effective resolutions is…
Did you know that over 43% of the web is powered by WordPress? That’s right, you’re about to join the ranks of millions who’ve chosen the world’s most popular content management system to…
In the dynamic world of digital marketing, the power of well-crafted content reigns supreme. Ranking-Articles.com emerges as a leader, providing exceptional content that not only engages readers but also propels websites to the…

In today’s digital landscape, encountering the ERR_CONNECTION_RESET error can disrupt the seamless flow of online activities. For those seeking innovative solutions to this challenge, understanding the underlying causes and implementing effective resolutions is…

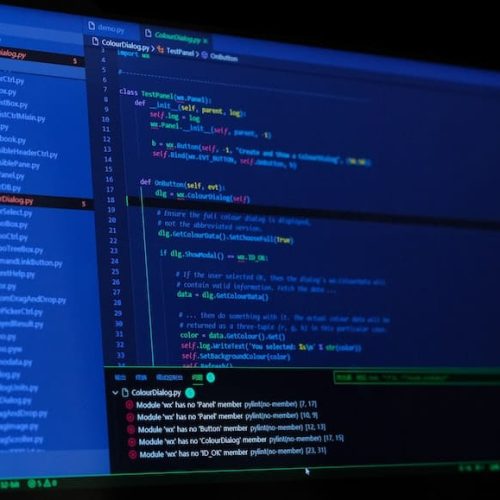
As businesses continue to seek innovative hosting solutions, the debate between cloud and VPS hosting has gained significance. Understanding the distinct advantages and drawbacks of each option is crucial for making informed decisions…

In the realm of modern database management systems, MariaDB and MySQL stand as two prominent players, each offering unique strengths and capabilities. This comparison delves into the key differences and essential insights necessary…

Encountering a 502 Bad Gateway error can disrupt the seamless flow of online operations, hindering the user experience and impeding business continuity. Addressing this issue requires a methodical approach, characterized by innovative problem-solving…

Encountering the 504 Gateway Timeout Error can disrupt the seamless functioning of a website, affecting user experience and potentially leading to loss of business opportunities. Addressing this issue requires a strategic and innovative…

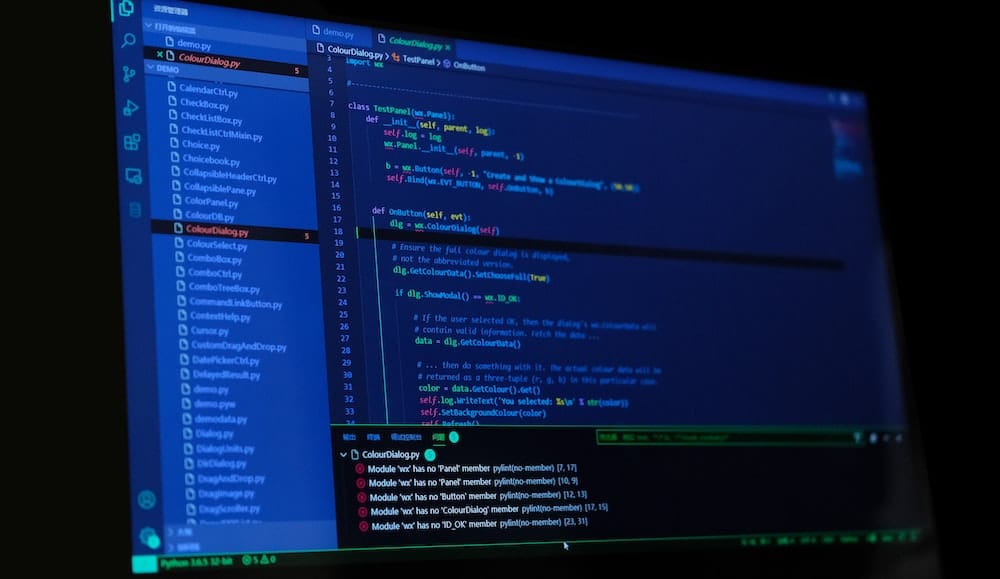
A content management system (CMS) is a digital platform that enables the creation, modification, and management of digital content. It empowers organizations to efficiently organize and publish content, facilitating seamless collaboration and workflow…

In the fast-paced digital landscape, encountering the 504 Gateway Timeout Error can impede user experiences and hinder business operations. Addressing this issue requires innovative solutions that align with the dynamic nature of web…

Content management systems (CMS) are the backbone of modern digital innovation, empowering businesses to efficiently organize, create, manage, and publish content across various digital platforms. Understanding the intricacies of CMS is pivotal for…